What Is a Rotating Proxy? How It Works and When You Need One
Most people think rotating proxies are about hiding. They're not.
Anonymity is a side effect. The real problem rotating proxies solve is infrastructure: a single IP address under scraping load fails fast. Send a few hundred requests from the same IP to any site with basic bot protection, and you'll hit a block, a rate limit, or a CAPTCHA wall before you've collected anything useful. Rotating proxies solve that by distributing your requests across a large pool of IP addresses automatically — no manual switching, no proxy lists to manage, no custom rotation logic in your code.
A rotating proxy is a server that automatically assigns a different IP address from a large pool for each request your script or application sends. Instead of all your traffic appearing to come from one IP, each request looks like it originates from a different device or location, preventing rate limits, IP bans, and CAPTCHA triggers at scale.
That's the definition. Here's how it actually works.
What Is a Rotating Proxy? The One-Paragraph Answer
A rotating proxy assigns a new IP address from a pool for every connection your application makes. Your script connects to a single endpoint. The gateway behind that endpoint selects an IP, forwards your request through it, and returns the response — all without your code doing anything differently than it would with a standard proxy.
Here's the mechanism in four steps:
- Your application sends a request to the proxy endpoint — one address, one port, your credentials.
- The gateway selects an IP from its pool based on availability, health status, and rotation logic.
- The request goes out through that IP. The target server sees that IP, not yours.
- The next request uses a different IP from the pool. The target server sees a different device.
From the target server's perspective, each request comes from a different user in a different location. No pattern forms. No threshold triggers. Your pipeline keeps running.
The Backconnect Gateway — What's Actually Happening Under the Hood
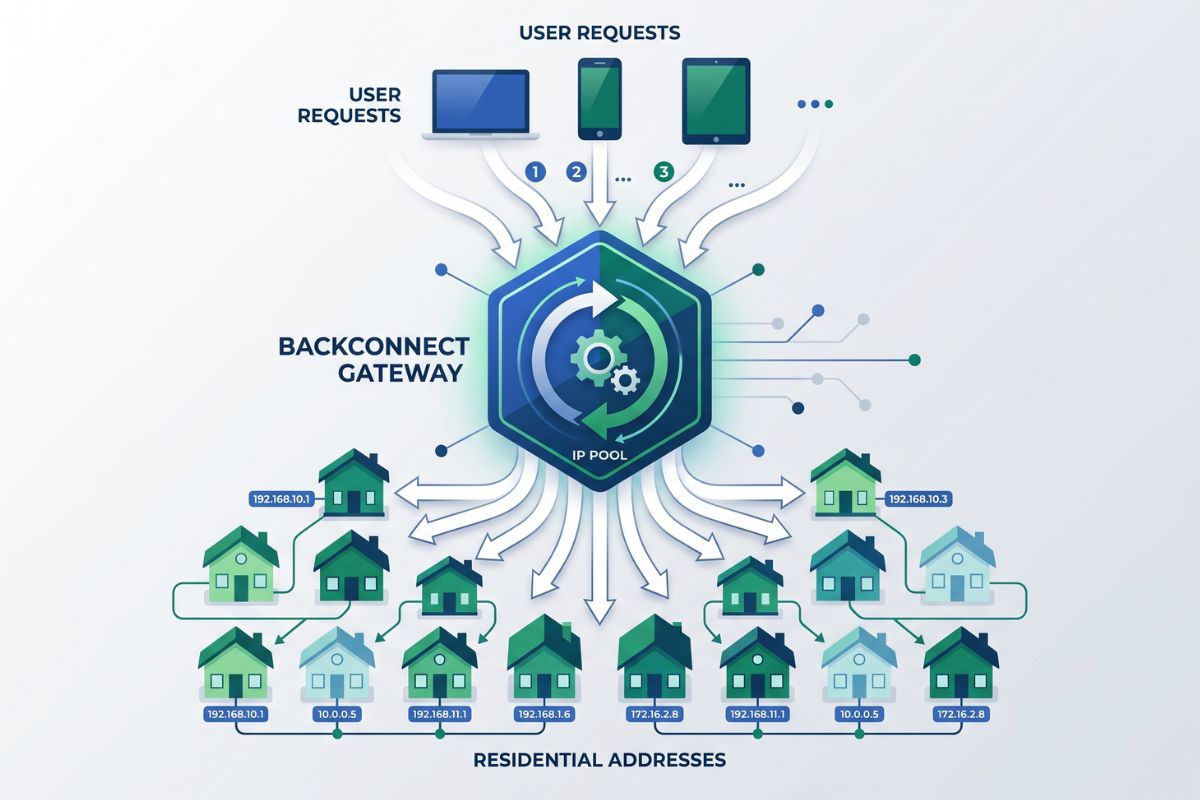
Every rotating proxy service runs on the same core architecture: a backconnect gateway. This is the part most guides skip, and it's the part that actually matters when something breaks.
What is a backconnect proxy?A backconnect proxy gateway is a single connection endpoint that routes outgoing requests through a rotating pool of IP addresses, handling IP selection and rotation transparently on behalf of the client application. Your code connects to one address. Everything behind that address — the pool, the health checks, the rotation logic — is invisible to your script.
Here's what that looks like in practice with Magnetic Proxy:
#python
# Configure rotating residential proxy through a single backconnect endpoint
import requests
proxy_user = "customer-youruser-cc-us" # country targeting encoded in username
proxy_pass = "yourpassword"
proxy_host = "rs.magneticproxy.net"
proxy_port = "443"
proxies = {
"http": f"https://{proxy_user}:{proxy_pass}@{proxy_host}:{proxy_port}",
"https": f"https://{proxy_user}:{proxy_pass}@{proxy_host}:{proxy_port}",
}
response = requests.get("https://ipinfo.io/json", proxies=proxies)
print(response.json())
# Output: different IP address on every executionEvery call to that endpoint routes through a different residential IP. Your script doesn't track which IP was used, doesn't rotate anything manually, and doesn't need to handle failed IPs — the gateway does all of that.
Magnetic Proxy's residential rotating network achieves a 99.95% average success rate and a 0.6-second average response time — measured across all requests routed through the backconnect gateway at rs.magneticproxy.net. (Source: Magnetic Proxy, 2026)
That 0.6-second latency is the real cost of routing through a residential device rather than a datacenter server. For most scraping pipelines, it's a tradeoff worth making. More on why below.
A rotating proxy works through a backconnect gateway: your application connects to a single endpoint, and the gateway selects a different IP from its pool for each outgoing request. This means your script sends thousands of requests through one connection string while appearing to originate from thousands of different devices.
Rotating Residential vs. Rotating Datacenter Proxies — What the Difference Actually Means
The proxy type matters more than most guides acknowledge. The mechanism of rotation is the same — a pool, a gateway, IP selection per request. What changes is the source of those IPs, and that source determines how anti-bot systems classify your traffic.
Anti-bot systems don't just check whether you're using a proxy. They classify every incoming IP by its ASN — Autonomous System Number. Datacenter IPs are registered to cloud providers: AWS, Google Cloud, Azure, DigitalOcean. Those ASNs are pre-flagged. The moment a request arrives from a known datacenter range, modern bot protection treats it with elevated suspicion before a single behavior signal is evaluated. (Source: Cloudflare, Bot Management, 2025)
Residential IPs are registered to ISPs — the same providers that connect homes and apartments to the internet. More importantly, those IPs carry the behavioral history of real users. That history is what passes bot scoring. A residential IP that has been used by a real person to browse, shop, and search looks fundamentally different to an anti-bot system than a clean datacenter IP that was spun up an hour ago.
Residential rotating proxies use IP addresses assigned by real Internet Service Providers to real home devices. Because these IPs carry the behavioral history of genuine users, anti-bot systems classify them as organic traffic rather than automated requests — which is why residential rotation achieves significantly higher success rates than datacenter rotation on protected targets.
Here's how the two compare in practice:
Some workflows need both: static IPs for authenticated sessions, rotating IPs for the bulk collection layer underneath.
How to Choose a Rotating Proxy Provider — 5 Things That Actually Matter
Generic "best proxy" lists are not useful. Here are the five factors that determine whether a rotating proxy actually works for your use case.
1. IP source — residential or datacenter, and how they're sourced.Residential IPs from real devices perform better on protected targets. Ask whether the provider discloses how residential IPs are obtained. Ethically sourced networks are less likely to have IPs that are already flagged from prior abuse.
2. Verified success rate on protected targets.A headline success rate means nothing without context. The relevant number is success rate on the types of sites you'll be hitting. Magnetic Proxy's rotating residential network achieves 99.95% across all requests — that's the number to benchmark against.
3. Geo-targeting precision.Country-level targeting is table stakes. For SEO rank tracking, price monitoring, and ad verification, city-level targeting is the differentiator. Confirm the provider supports country, region, and city targeting natively — not as an add-on.
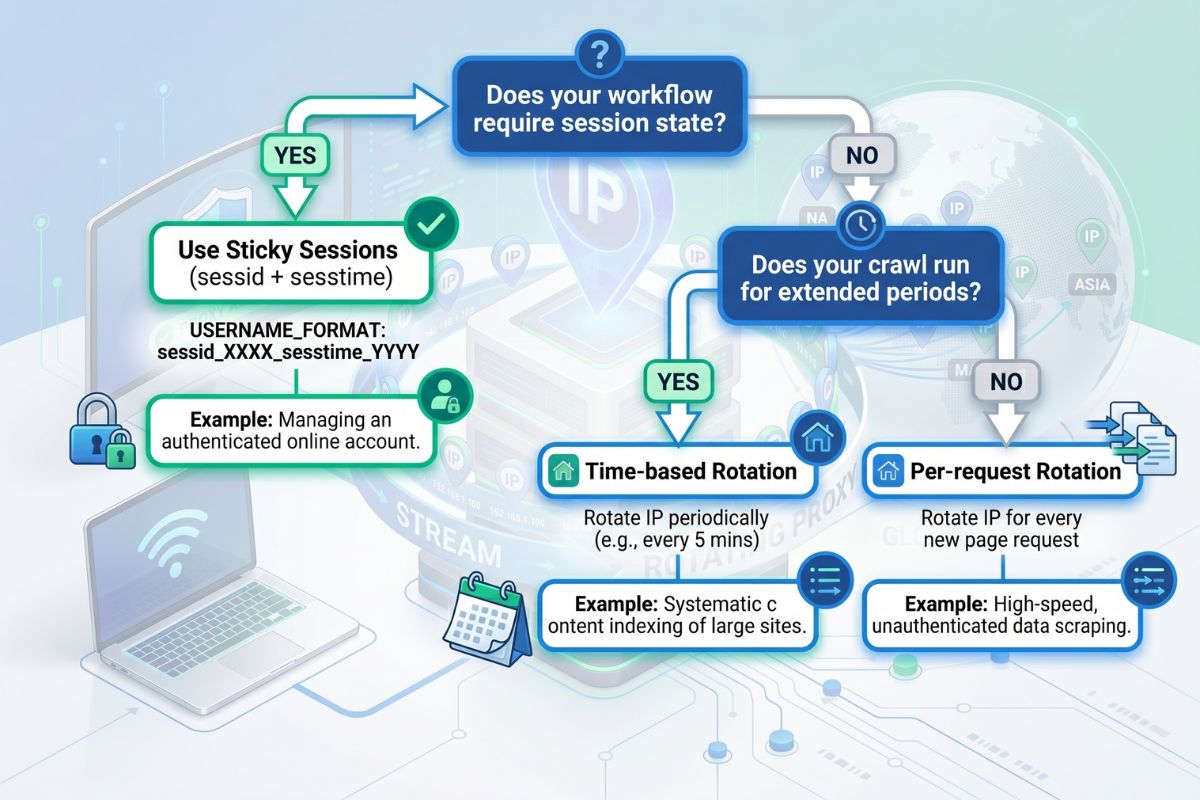
4. Session control.Can you configure sticky sessions with a custom duration, or is rotation all-or-nothing? For any workflow with session state, you need sessid and sesstime equivalents — the ability to hold an IP for a defined window without hard-coding a specific IP address.
5. Protocol support.HTTP and HTTPS cover most use cases. SOCKS5 handles non-HTTP traffic — useful for tools and applications that need lower-level network routing. SOCKS5h adds proxy-side DNS resolution, which prevents DNS leaks for workflows where that matters.
Magnetic Proxy's rotating residential proxies cover all five — starting at $5/month for a test run with no commitment.
The Infrastructure Problem Nobody Talks About
Rotating proxies are not a privacy tool dressed up as infrastructure. They are infrastructure — the layer that makes high-volume, reliable data collection possible at scale.
The mechanism is straightforward: one endpoint, one pool, automatic selection per request. The decision that determines whether your pipeline succeeds or fails is not whether to use rotation — it's which rotation strategy matches your workflow. Per-request for volume, sticky sessions for state, time-based for long-running crawls.
Get the strategy right, and the rotating proxy becomes invisible — which is exactly what good infrastructure should be.
See Magnetic Proxy's rotating residential proxy plans and start a test run.
Frequently Asked Questions
Check the most Frequently Asked Questions
What is a rotating proxy?
What is the difference between a rotating proxy and a static proxy?
How does proxy rotation work?
Are rotating proxies legal?
When should I use sticky sessions instead of rotating proxies?
Latest Posts
Here’s how Profile Peeker enables organizations to transform profile data into business opportunities.



.png)