What Is a Residential Proxy and How Does It Work?
Your IP just got banned again. The CAPTCHA walls are multiplying, your scraping pipeline is returning error codes instead of data, and every datacenter proxy you try gets flagged within minutes. The problem is not your code. It is your IP address, and switching to another datacenter server will not fix it. This guide explains exactly what residential proxies are, how the routing works at a technical level, and the one question you must ask every provider before you hand them your money.
What Is a Residential Proxy? (The Definition That Actually Matters)
A residential proxy is an intermediary server that routes internet traffic through a real IP address assigned by anISP to a homeowner's device. Because these IPs belong togenuine consumer Autonomous System Numbers (ASNs), targetwebsites treat them as organic traffic, giving themsignificantly higher trust scores than datacenter IPs.
How it works:
- You send a connection request.
- The proxy routes it through a physical home device.
- The target website sees a regular human user.
- Your actual IP address remains completely hidden.
The reason this matters technically comes down to trust scores. Every IP address on the internet belongs to an Autonomous System Number (ASN), which is essentially a registered block of IPs assigned to a specific organization. Consumer ISPs like Comcast, AT&T, and Verizon operate consumer ASNs. Cloud providers like AWS, DigitalOcean, and Google Cloud operate commercial ASNs.
Anti-bot systems know the difference. A request arriving from a commercial ASN triggers immediate scrutiny. A request arriving from a Comcast residential block looks, to every detection layer the target site runs, like a person sitting at home browsing the internet. That distinction is the entire value proposition of a residential proxy, and it is why IP trust score is the metric that actually predicts whether your requests get through.
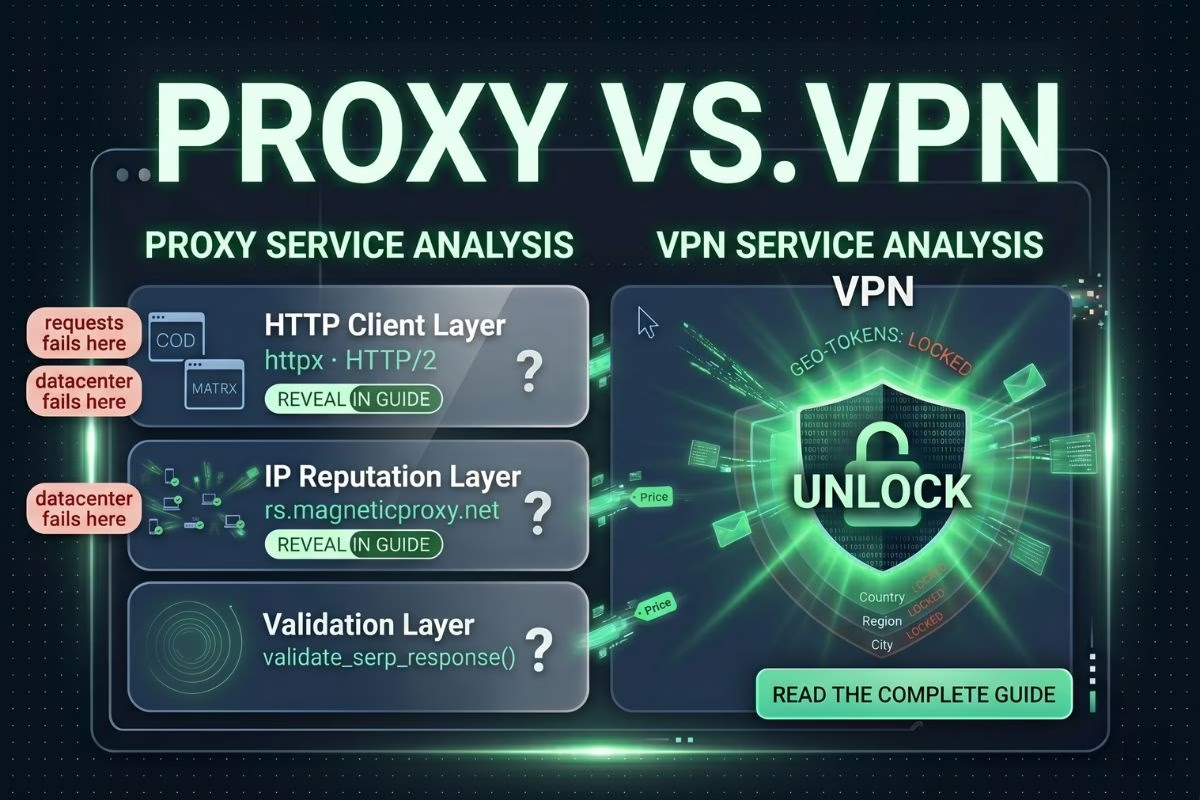
Residential Proxies vs. Datacenter Proxies: Why the Difference Destroys Your Block Rate
Datacenter proxies are faster and cheaper. They are also the first thing every serious anti-bot system blocks by default.
The block rate difference is not marginal. Datacenter IPs sitting in commercial ASN ranges are flagged automatically by web application firewalls (WAFs), CAPTCHA providers like Cloudflare and Akamai, and browser fingerprinting systems that cross-reference IP reputation databases. It does not matter how sophisticated your request headers are. The moment your traffic originates from an AWS IP block, you are already suspect.
Here is how the two options compare across the dimensions that matter in production:
The block rate figures are not theoretical. Imperva's Bad Bot Report documents how advanced bots using residential ISP addresses consistently bypass WAF detection at rates that datacenter proxies cannot approach.
What Are ISP Proxies (And Why They're Not the Same as Residential)
Here is where the industry gets deliberately confusing, and where a lot of buyers get burned.
ISP proxies are datacenter servers that have been registered under consumer ASN ranges to mimic the appearance of residential IPs. They are faster than true residential proxies because they run on server hardware, not home devices. Providers market them aggressively as "residential-grade" or "ISP-quality" because the margin is better.
They are not the same thing. A sophisticated anti-bot system that cross-references ASN registration dates, IP velocity patterns, and behavioral signals will eventually distinguish an ISP proxy from a true peer-to-peer residential IP. For low-to-medium security targets, ISP proxies work fine. For enterprise-grade targets running advanced bot mitigation, they fail at the same rate as datacenter proxies once the detection models are trained on them.
The rule is simple: if the provider cannot show you that the IPs come from real devices with real owners, you are not buying residential proxies. You are buying datacenter proxies with better marketing.
How Residential Proxies Actually Work: The Request Lifecycle
Understanding the routing architecture matters when you are debugging failures and optimizing session performance.
- Your client sends a request to the proxy provider's gateway.
- The gateway selects an available peer device from the residential IP pool.
- Your request routes through that device's real ISP-assigned connection.
- The target website receives the request from the peer device's residential IP, not yours.
- The response travels back through the same path to your client.
Your actual IP address is never exposed at any point in the chain.
The two session configurations you will encounter in every serious provider:
Rotating proxies assign a new IP address to each request or at a defined interval. This is the configuration for high-volume scraping, price monitoring, and any operation where appearing as many different users is more important than maintaining session continuity. IP rotation is the default configuration for most scraping deployments.
Sticky sessions (also called static residential proxies) hold the same IP address for a defined duration, typically between 1 and 30 minutes. This is the configuration for operations that require session state: logging into accounts, completing multi-step checkouts, managing social media profiles, or any workflow where the target site tracks session cookies. Switching IPs mid-session breaks authentication and triggers fraud flags.
Protocol support matters too. Most enterprise-grade residential proxy networks support both HTTP/S and SOCKS5. SOCKS5 is the preference for non-HTTP traffic and applications that need lower-level socket control. If your use case involves anything beyond standard web requests, confirm SOCKS5 support before committing to a provider.
See how a real residential proxy network performs on your target sites. Start your free trial — no commitment required. Get started →
The Dirty Secret the Proxy Industry Doesn't Want You to Know
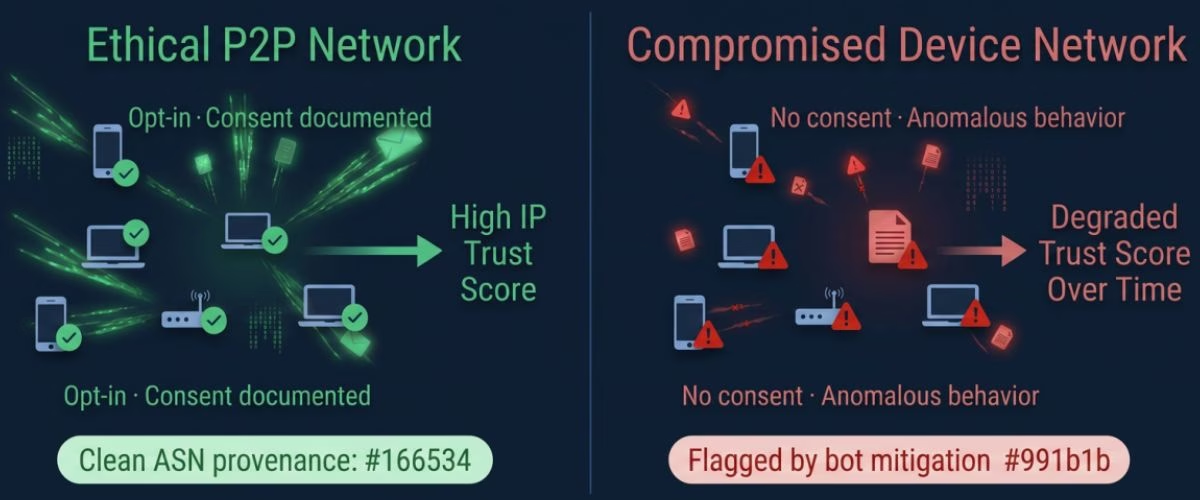
True residential proxy networks rely on peer-to-peer (P2P) bandwidth sharing, where device owners explicitly opt-in to share their idle internet connection. Because these IP addresses belong to consumer Autonomous System Numbers (ASNs) rather than commercial server farms, they maintain the highest possible IP trust scores. Consequently, enterprise residential proxies experience a block rate of less than 1% when interacting with aggressive bot mitigation systems, whereas traditional datacenter proxies are routinely blocked by default.
Why does ethical sourcing matter for residential proxy performance?
Because the IP trust score of a residential proxy degrades the moment detection systems identify behavioral anomalies associated with non-consenting devices. Compromised devices, meaning devices enrolled in a proxy network without the owner's knowledge, exhibit different traffic patterns than voluntarily participating ones. They show unusual bandwidth consumption at odd hours, inconsistent geographic activity, and connection signatures that advanced bot mitigation systems have learned to flag.
The Internet Assigned Numbers Authority (IANA) governs how ASN blocks are distributed to ISPs and commercial entities. This public registry is what anti-bot vendors use to build their IP reputation databases. A residential IP from a legitimate consumer ISP has a provenance trail. A datacenter IP masquerading under a consumer ASN does not, and the anomaly eventually surfaces.
Warning: If a proxy provider cannot show you explicit documentation of how device owners opt into their network, assume the IPs are sourced from compromised devices. Routing your enterprise traffic through a botnet is not just an ethical problem. It is a legal liability that your legal team needs to know about before your next scraping deployment.
The Electronic Frontier Foundation has established digital privacy standards that make this distinction legally significant in US jurisdictions. Using a service that enrolls devices without consent potentially implicates your organization in unauthorized computer access statutes, regardless of whether you were aware of the sourcing method.
Ask the hard question before you sign. If the provider deflects, walk away.
The Highest-Value Use Cases for Residential Proxies in 2026
Most use case lists in this space are generic. Here is what actually happens in production.
A price intelligence team running competitive monitoring against a major US e-commerce retailer came to us after their datacenter proxy setup had become unusable. They were executing roughly 35,000 product page requests per day across six competitor domains. Their block rate using a rotating datacenter proxy pool had climbed to 81% over three months as the retailer's bot mitigation vendor updated its detection models. The pipeline was returning cached or error pages instead of live pricing data, which meant the intelligence feeding their repricing algorithm was stale by hours.
After migrating to a rotating residential proxy pool with geo-targeted US-state-level IP selection, their block rate dropped to 0.9% in the first week. The same requests, the same target domains, the same request frequency. The only change was the IP origin. That is what a consumer ASN does for you that a datacenter ASN cannot.
The use cases where residential proxies consistently outperform every alternative:
Web scraping at scale. Any web scraping at scale operation targeting protected domains — retail, travel, financial data, social platforms — requires residential IPs to maintain acceptable success rates past the first few thousand requests.
Sneaker bots and automated checkout. High-demand product releases on Nike, Adidas, Supreme, and similar platforms use aggressive bot detection specifically tuned to flag datacenter IP ranges. Residential rotating IPs are the baseline requirement for any checkout automation with real conversion expectations.
Ad fraud verification. Verifying that your ads display correctly in specific geographic markets, and that they are not being served in brand-unsafe environments, requires residential IPs in the target region. Datacenter IPs in the same region often get served different ad inventory than real consumers.
SERP rank tracking. Checking search rankings from the perspective of a user in a specific city or zip code requires residential geo-targeting. Search results personalize aggressively by location, and datacenter IPs return results that do not reflect what real users in that market see.
Geo-targeted content access. Streaming platforms, news sites, and financial data providers serve different content by geography. Accessing region-locked content for research, compliance verification, or QA testing requires residential IPs in the target jurisdiction.
How to Choose a Residential Proxy Provider Without Getting Burned

The proxy market has dozens of providers and almost no standardized way to evaluate them. Here is the framework that actually separates trustworthy providers from those selling you repackaged datacenter IPs.
Criterion 1: IP sourcing transparency. This is non-negotiable and should be the first question you ask. A legitimate P2P residential proxy provider can show you their device enrollment flow, their opt-in consent mechanism, and their terms of service for participating device owners. If the sales team cannot answer this question in the first conversation, the answer is no.
Criterion 2: Pool size and geographic coverage. Pool size matters because IP addresses get flagged over time. A provider with 5 million IPs in the US rotates through its pool faster than one with 50 million, which increases the per-IP detection risk on high-volume operations. For serious enterprise use cases, you want a provider with at minimum 10 million verified residential IPs across your target geographies.
Criterion 3: Session type flexibility. The provider must support both rotating and sticky sessions with configurable session duration. If they only offer one mode, you are buying a product built for one use case, not an infrastructure tool.
Criterion 4: Protocol support. HTTP/S and SOCKS5 as standard. If SOCKS5 is an add-on or unavailable, the network is not built for enterprise workloads.
Criterion 5: Pricing model transparency. Bandwidth-based pricing is standard for residential proxies. Be cautious of providers offering unlimited bandwidth at fixed prices on residential networks — the economics do not work unless they are throttling your sessions or rotating you onto lower-quality IPs during peak periods.
According to Imperva's Bad Bot Report (2024), advanced persistent bots using residential ISP addresses bypass detection at a rate 4.7 times higher than those using datacenter infrastructure. (Source: Imperva, 2024.) That data point is why sourcing transparency is criterion one, not criterion five. The performance advantage of true residential proxies only exists if the IPs are genuinely residential.
If you want a provider that can show you opt-in documentation before you sign a contract, verify that the network is built entirely on peer-to-peer consent before committing a production budget.
The IP Origin Problem Nobody Talks About Upfront
The gap between a 0.9% block rate and an 81% block rateis not a configuration problem. It is an IP originproblem. Datacenter proxies are cheap for a reason:they are the first thing every serious anti-bot systemis trained to detect and reject. Residential proxieswork because consumer ASNs carry trust scores thatcommercial server farms cannot replicate.
The residential proxy market has its own trap, though.ISP proxies masquerading as residential, and providerssourcing IPs from compromised devices without ownerconsent, are common enough that due diligence is notoptional. The five-criterion framework in this guideexists because buying the wrong product does not justwaste budget, it can expose your organization to legalrisk that no proxy pool is worth.
Ask for the opt-in documentation. Check the ASNclassification. Verify the pool size against yourvolume requirements. Then run a test batch against youractual target domains before committing to a contract.
The block rate will tell you everything you need to know.
Frequently Asked Questions
Check the most Frequently Asked Questions
What is a residential proxy and how is it different from a datacenter proxy?
Are residential proxies legal to use?
What is IP rotation and why does it matter for residential proxies?
How do I know if a residential proxy provider is using ethically sourced IPs?
What is the difference between rotating and sticky session residential proxies?
Latest Posts
Here’s how Profile Peeker enables organizations to transform profile data into business opportunities.



.png)